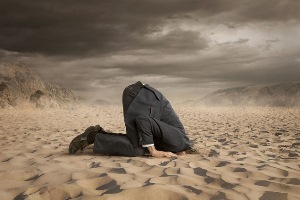
No more ‘heads in the sand’ as security firms urge customers to patrol enlarged attack surface
Security never seems to get any easier, does it? Ransomware, say the experts, shows no signs of diminishing as a threat to consumers and enterprises. So if they can’t nullify the threat, how can enterprises and consumers reduce their vulnerability? Security specialists advise Jeremy Cowan on the next steps to take.
Luke Somerville, head of Special Investigations at Forcepoint, says, “The most effective strategy to stop ransomware attacks relies on preventing the malicious actor from ever gaining access to your devices. While the number of applications and services that individuals use for both their work and personal lives continues to increase, so does the number of cyber threats, making the network more vulnerable.
“As threat actors become more skilled, it is crucial for organisations to take a threat-centric and operational approach to security. This leads to the reduction of complexity and fragmentation, while providing superior visibility, continuous control, and advanced threat protection across the entire attack continuum. In short, organisations need to start thinking holistically about their security platform,” says Somerville.
“It is no longer an option for organisations to bury their heads in the sand.”
He believes the sheer volume of devices connected to the web makes it easy for attackers to identify and exploit poorly defended entry points to private networks. It is, therefore, no longer an option for organisations to bury their heads in the sand: they need to protect their devices, protect their personal data and, fundamentally, put measures in place to protect their privacy before it’s too late.
(Also see: NotPetya ransomware Frequently Ask Questions)

Increased attack surface
According to James Romer, EMEA chief security architect at SecureAuth Corporation: “Sustained changes to the ways employees work with the rise in remote working and bring your own devices (BYOD) has meant that the attack surface area that organisations have to protect and defend has increased significantly.”
This, combined with lax policies, he believes, leads to an identity sprawl of access and sensitive data, which poses a significant risk to the enterprises as attackers look to exploit vulnerabilities to get a foothold into the network.

James Romer
Romer adds, “Organisations need to make sure only the right people get in while also maintaining a frictionless user experience. By preventing stolen or compromised credentials from gaining access, the applications and device being used suddenly becomes irrelevant. Modern identity and access management approaches, such as adaptive authentication is a key component of this. It uses adaptive access control techniques and identity-based detection that work invisibly to the user, but protect against, detect and remediate attacks rendering stolen credentials useless.”
David Kennerley, director of Threat Research at Webroot is also focused on the attack surface. “IoT (the Internet of Things) has allowed many industries to transform how they operate, communicate and collaborate,” he says, “and adoption has been largely enabled by improved network connectivity. However, the array of connected devices represents a large potential network attack surface, that when compromised could grant an attacker access to sensitive and highly valuable data.”
Devices not designed securely
“Whereas we now understand the concept of building in security at the design stage – as shown when producing PCs, laptops and the ever-increasing security built in to smart phones – many IoT devices are not designed with security in mind.”
Businesses and consumers alike, are often not aware their devices are susceptible to vulnerabilities already being targeted in the wild, and even when they are aware, many IoT devices are difficult to update and security configure. Kennerley points out that compromising these devices can lead to further network attacks, data and communication theft, as well as being recruited as a weapon in huge botnets, awaiting the next command.

David Kennerley of Webroot
“Businesses need to understand the risks of adding more and more IoT devices to the network and the possible consequences of being compromised. Understanding how and what a device collects, stores and communicates is crucial to securing sensitive data. Routinely checking for the latest updates for their devices is important and resetting firmware periodically isn’t a bad idea. Ultimately, making sure IoT devices are configured to be as secure as possible is essential – it’s bye, bye to the ‘Set-up and forget’ mentality. These devices and the network as a whole need to be continuously monitored, utilising the latest threat intelligence solutions,” Kennerley insists. “By employing an informed and tactical approach, it will pay dividends towards keeping the whole organisation’s environment safe.”
Understand where your data is
Somerville adds, “Organisations can spend substantial sums on the latest cybersecurity technology designed to identify and mitigate threats when they emerge, but they will always be at significant risk if they do not find ways to understand where their data is, who is accessing it, and can identify changes in behaviour to mitigate the risk accordingly.”
By understanding the human point, he believes, people can adapt their security postures to fight emerging threats and create an environment with security at its core, ensuring that trust in IoT devices is built-in.
“With an understanding of the value of the data that is flowing through the network, organisations can protect their fragmented systems and ensure that they can identify and mitigate risk regardless of where it sits on the network. By turning the process around and focusing on the behavioural patterns associated with attacks, rather than the specifics of individual attacks, we can adapt to the changing threat environment and prepare for the next attack rather than the last one,” Somerville concludes.

The author is Jeremy Cowan, editorial director & publisher of IoT Now, IoT Global Network, and VanillaPlus.
Comment on this article below or via Twitter @IoTGN
