Mirai botnet shows just how vulnerable the IoT really is

Alan Grau, president and co-founder of Icon Labs
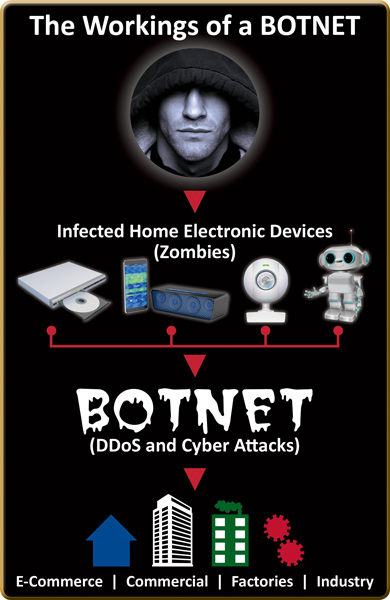
Internet-based attacks are on the rise and, increasingly, these attacks target IoT devices like DVRs, web cams, and appliances.
Cyber-criminals, hacking bots, industrial or international espionage agents, and even terrorist groups are now targeting industrial, military, automotive, medical, utility systems, and ultimately the internet itself, as demonstrated by the recent cyber-attack directed at Dyn (a domain name system host). The attack caused an outage in internet services for numerous large-scale internet-based companies.
How did this happen? In September, the creator of Mirai, malware that converts IoT devices into bots, released the source code thereby allowing anyone to build their own botnet army made of IoT devices. The botnet searches for devices that have weak factory default or hard-coded user names and passwords, all of which are particularly vulnerable to attack. Once the devices have been identified and turned into bots, they can be directed to attack a single source, thus crippling its ability to function, says Alan Grau is president and co-founder of Icon Labs.
On October 21, 2016, a botnet comprised of millions of these devices attacked Dyn, causing a significant outage of internet services. This may be one of the first large-scale attacks using IoT devices, but it is certainly not the last. With millions of unprotected IoT devices, we are vulnerable to a major attack that could considerably impact the internet infrastructure, and possibly bring it to a standstill.
This time it was relatively contained to one company, but next time it could be bigger and more damaging. Even scarier, this botnet is still in existence and it will be almost impossible to defuse future attacks, at least not until existing devices are updated with new security features.
This attack didn’t have to happen. OEMs can build in protection at the device-level that will protect against a botnet attack. Building protection into the device itself provides a critical security layer.
Given these new security capabilities, the devices are no longer depending on the user (in home, non-technical consumers) to update the user name and password as the sole layer of security. In addition, the security can be customised to the needs of the device.
Many of today’s modern IoT devices are mini-computers connected to numerous other vulnerable devices. Including security in these devices is a critical design task. Security features must be considered early in the design process to ensure the device is protected from the advanced cyber-threats they will be facing.
It’s imperative that we address this problem, as evidenced by the recent notice from the Department of Homeland Security, which issued a warning about attacks from the Internet of Things following the release of the code for Mirai. They are worried and you should be too.
The author of this blog is Alan Grau is president and co-founder of Icon Labs.
Comment on this article below or via Twitter @IoTGN